What Is an AI Security Graph?
Security exploits nowadays depend on chaining relationships across identities, services, and infrastructure. So not only do you need strong signals, but strong context as well. AI security graphs resolve this by modeling systems as connected structures and analyzing how relationships constitute attack paths. That’s what we are going to discuss in this post today: what AI security graphs are, how they work, and why they are becoming increasingly relevant.
What Is an AI Security Graph
An AI security graph is a data model that represents security-relevant entities and their relationships as a graph, then applies machine learning or statistical techniques to analyze that structure.
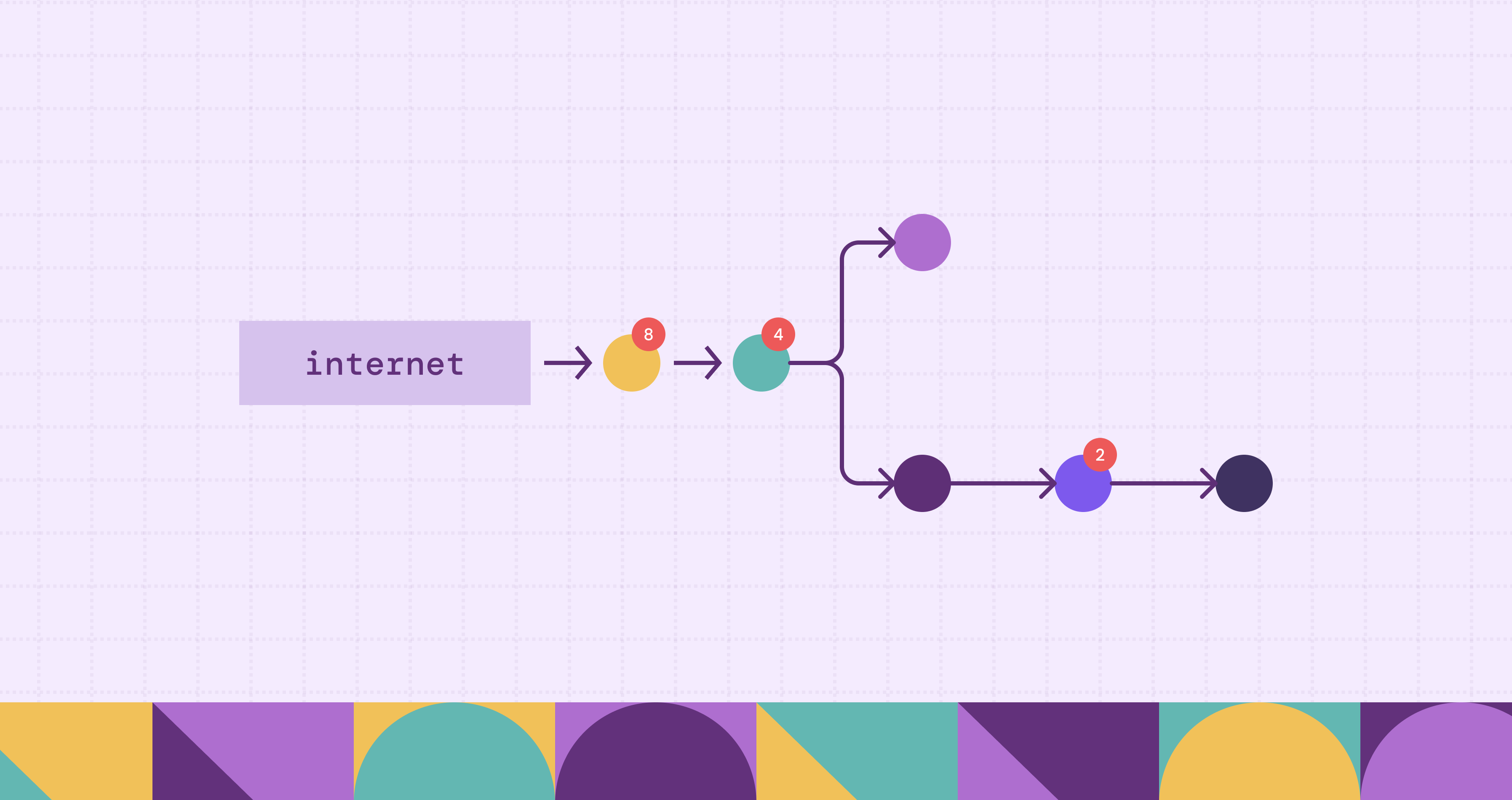
A security graph consists of nodes and edges. Nodes represent various entities, for example, users, roles, virtual machines, containers, databases, APIs, or network segments. Edges represent relationships between those entities. These relationships include permissions, network access, trust boundaries, API calls, and configuration links. For example, an IAM role may have permission to access a storage bucket, or a container may communicate with a database over a specific port. Each of these connections becomes an edge in the graph.
The resultant structure near identically corresponds to how real-world attacks transpire.
Attackers, seldom exploiting a single vulnerability, move through systems by chaining relationships. A compromised identity might access another service, escalate privileges, and eventually reach sensitive data. A graph captures these multi-step paths, making it possible to reason about reachability, which is a core concept in security: can one entity reach another, and through which sequence of steps?
The “AI” layer builds on top of this graph structure for analysis, through techniques like path ranking, anomaly detection, and pattern recognition. For example, an AI model might assign higher risk scores to paths that combine excessive permissions with exposure to the internet. It might also detect unusual access patterns that deviate from historical behavior.
An AI security graph also unifies data from multiple sources into a single representation. Security data is typically fragmented across logs, identity systems, cloud configurations, and network telemetry. Each system provides partial visibility. A graph connects these fragments into a coherent structure.
You will build AI security graphs by mapping existing data sources into graph structures. To that end, you will want to avoid duplicating data or maintaining separate graph databases. A more much more pragmatic and sensible option would be to define graph schemas over existing datasets and query them directly (PuppyGraph makes this really easy). You will have minimal pipeline complexity and at the same time have the graph aligned with the current state of the environment.
How AI Security Graphs Work
AI security graph, from fragmented security data, forms a connected structure augmented by machine learning where you can run queries. We can look at its build process in four distinct stages.
1. Data Ingestion from Security Systems
Usually, you will have raw data across multiple disparate sources, for example:
- Identity systems (IAM policies, roles, users)
- Cloud configurations (VPCs, security groups, storage permissions)
- Network telemetry (flows, connections, exposed endpoints)
- Application and API logs
- Endpoint and workload metadata
From these sources, you will ingest all the data into a single source which initiates the graph building process. However, you can avoid heavy ETL pipelines and instead connect directly to existing data stores, like data warehouses, lakehouses, or log systems, and use them as the source of truth. You keep the graph aligned with the current state of the environment while averting delays batch processing causes.
2. Graph Modeling and Schema Definition
The next step, after connecting all data sources, defines how data maps into a graph through a graph schema. The schema specifies, for example:
- Vertex types: users, roles, VMs, containers, databases, APIs
- Edge types: “has access to,” “connected to,” “assumes role,” “exposed to internet”
- Properties: attributes like IP address, privilege level, or configuration state
The schema defines what entities exist and how they relate. In security contexts, you might often call it an ontology. It provides a consistent model across otherwise disconnected systems.
A well-defined schema, in addition to organizing data, constrains queries so you can traverse only valid relationships, thereby reducing ambiguity. It ensures that both analysts and automated systems operate on a consistent interpretation of the environment.
3. Query Execution and Traversal
With the graph defined, teams can run queries that traverse relationships across multiple systems. These are multi-hop queries: each hop represents a step in a potential attack path.
Here are some examples:
- “Which public-facing assets can reach a sensitive database?”
- “What paths allow this IAM role to escalate privileges?”
- “Which workloads share network access with compromised resources?”
To satisfy these queries, the system follows edges between nodes and thus traverses the graph, giving you efficient exploration of deep relationships, even across billions of connections.
Modern graph engines support query languages like Cypher or Gremlin. These languages express patterns intuitively with great flexibility, making complex relationship queries easier to write and reason about.
Some systems execute these queries directly on existing datasets without copying them into a separate graph store. This avoids duplication and allows queries to reflect real-time state changes in the underlying data.
4. AI-Driven Analysis on Graph Structures
The final layer applies AI and statistical techniques to the graph for actionable insights. Here are some common techniques for this:
- Path scoring: Rank attack paths based on factors such as exposure, privilege level, and asset sensitivity
- Anomaly detection: Identify unusual relationships or traversal patterns that deviate from baseline behavior
- Pattern matching: Detect known attack patterns, such as privilege escalation chains or lateral movement sequences
These techniques, contrary to disjointed logs in traditional models, operate on graph topology. They consider how entities connect in addition to the occurred events.
In more advanced setups, like in PuppyGraph, AI agents interact directly with the graph. They use the schema as a guide to generate queries, validate them against defined relationships, and refine their analysis based on structured feedback. This allows systems to iteratively explore the graph and build a more thorough understanding of the environment.
AI Security Graph vs Traditional Security
Modern cyber-offences progress across identities, workloads, permissions, network paths, and misconfigurations. An AI security graph treats these connections as first-class data. In traditional security, you can’t model such linkages; so you force analysts to reconstruct those relationships after the fact.
Here’s a brief illustration comparing the two approaches:
Think about this example scenario where a conventional tool alerts on a publicly exposed VM, an overprivileged role, or a misconfigured security group, but as separate issues. An AI security graph, however, connects those findings and demonstrates that they conceive an accessible route to a sensitive asset.
All of this does not make traditional security tooling obsolete; SIEMs, EDR platforms, CSPM tools, and identity systems still generate the raw signals necessary. But most of them answer narrow questions inside their own domain. A graph-based method sits above those sources and connects their outputs into a structural view of risk.
The AI layer alters the kind of analysis you can execute on that structure. You not only ask whether an event looks suspicious, but also whether a route is plausible, whether a privilege chain is unwonted, or whether a union of conditions creates exposure. Thus such “relationship-aware” reasoning takes you closer to how attackers in effect operate.
Why Cloud Environments Break Traditional Detection
Most legacy approaches assume systems are relatively stable, have well-defined boundaries, and changes happen in controlled intervals. None of these assumptions hold in modern cloud infrastructure.
Ephemeral Infrastructure Removes Stability
Cloud resources do not persist long enough to build reliable baselines. For example:
- Instances scale up and down automatically.
- Containers start and stop in seconds.
- Serverless functions execute and disappear.
- IP addresses and network identities change frequently.
As a result, any detection logic that depends on static inventories or historical baselines becomes unreliable.
Traditional systems often rely on periodic scans or snapshots. These methods capture a point-in-time view. But in cloud environments, that view becomes stale almost immediately. Detection systems end up reasoning about infrastructure that no longer exists or missing resources that were created after the prior scan.
Identity Becomes the Primary Attack Surface
In cloud systems, identity replaces the network perimeter as the main control plane. Users, roles, service accounts, and tokens define what actions are allowed. Permissions can be chained across services, accounts, and regions. A single identity may assume multiple roles, each granting different levels of access.
So a misconfigured role might not be dangerous on its own. But when combined with other permissions, it can enable privilege escalation or lateral movement. Traditional detection tools often evaluate these configurations in isolation, missing how permissions combine across systems.
Cross-Service Relationships Increase Latent Risk
Cloud services are deeply interconnected. A compute instance may access a storage bucket. That bucket may trigger a serverless function. The function may write to a database. Each of these interactions creates a path that can be exploited.
In cloud services, since they are so interconnected, each interaction can create a route that can be exploited. For example, a compute instance may access a storage bucket, which triggers a serverless function that writes to a database.
You can seldom see such relationships in a single system. They span IAM policies, network rules, and service configurations. Conventional tools, since they analyze each domain, makes it difficult to detect multi-step attack paths that cross service boundaries.
Continuous Change Outpaces Detection Pipelines
Cloud environments continuously change. Infrastructure-as-code updates configurations automatically. Permissions evolve as teams iterate on features. You have to deal with new risks at a pace that traditional detection pipelines cannot match.
Many systems do batch processing or scheduled updates, so there is some delay. In fast-moving environments, this delay creates blind spots and by the time a risk is detected, the underlying configuration may have already changed.
Lack of Global Context Limits Decision-Making
Each security tool sees only part of the system, for example:
- IAM tools understand permissions.
- Network tools understand connectivity.
- Vulnerability scanners elucidate software weaknesses.
Exploits, not respecting such boundaries, combine identity, network access, and misconfigurations into a single route. Without a unified view, you must manually correlate signals across tools, a process that is slow and error-prone, especially under time pressure.
How AI Security Graphs Transform Cybersecurity
AI security graphs change how teams detect, investigate, and respond to threats.
From Alerts to Attack Paths
Traditionally, you get an alert about a potential issue and then try to determine whether these signals connect to something meaningful. AI security graphs evaluate whether existing relationships constitute a viable attack path. As a result, you can find out whether a chain of conditions leads to a compromise.
This approach reduces the need to manually correlate signals. The graph already encodes how entities connect. AI models can then rank paths based on various factors: exposure, privilege level, asset sensitivity, and so on.
Prioritizing Exploitable Risk
Not all vulnerabilities or misconfigurations carry the same risk. Many findings remain theoretical because no path leads to a critical asset. AI security graphs help identify which issues are actually exploitable in the current environment.
So when it comes to prioritization, instead of fixing issues based on merely severity scores, you can focus on conditions that precipitate real attack paths. This results in more efficient remediation and better use of engineering time.
Accelerating Investigations
Incident response depends on understanding how an attacker moved through a system. So you have to stitch together logs, alerts, and configuration data from multiple tools.
With a graph-based approach you have much shorter processes. Analysts can traverse the graph to trace how an identity accessed a resource, what permissions enabled that access, and which systems were involved along the way.
This lessens the cognitive load on analysts. You don’t have to reconstruct the system from fragments, but only explore a model that already reflects how components interact. Investigations become more direct and less dependent on manual correlation.
Enabling Continuous Security Reasoning
As already discussed, cloud environments are often ephemeral, dynamic, and short-lived. AI security graphs support continuous reasoning by operating on up-to-date relationships. You can evaluate risk as the environment evolves, detecting novel attack paths as they emerge.
This capability, however, depends on how you have built the graph. Systems that rely on heavy data pipelines introduce delays between data generation and analysis. Newer approaches, like in PuppyGraph by dint of graph structures being directly over existing data sources, have minimal lag and keep the model aligned with current state.
Benefits of AI Security Graphs
Let’s briefly discuss the benefits of AI security graphs that become apparent at the level of data, architecture, and long-term maintainability.
Real-Time Security Posture
AI security graphs enable real-time security by operating on up-to-date relationships. When the underlying data changes, the graph reflects those changes immediately or with minimal lag. This allows teams to reason about risk based on the current state of the system and not a snapshot from minutes or hours ago.
Unified Model Across Security Domains
Security data is fragmented across multiple systems, as we’ve already mentioned. You have identity platforms that manage permissions, network tools for connectivity, and cloud platforms for infrastructure. Each system exposes its own interface and data model. It’s difficult to reason about risk across domains.
AI security graphs give you a unified representation. You don’t need to switch between tools and reconcile different formats. Teams can query relationships across domains without manually consolidating data.
Scalability with Growing Data Volume
Large environments generate billions of events and relationships across users, services, and infrastructure. If you do repeated joins or batch processing, you will often struggle to scale under this load. Graph-based approaches handle this growth more efficiently as they are designed to traverse relationships across large datasets, even when queries involve multiple hops. Distributed graph engines can scale horizontally, allowing teams to analyze complex environments without degrading performance.
Alignment with AI and Automated Systems
AI systems need structured context to produce authentic results. Since relational schemas encode relationships indirectly, this makes it harder for automated systems to interpret how data connects. AI security graphs overtly expose these relationships through a defined schema.
The structure therefore also acts as a foundation for automation. AI models and agents can generate queries, validate them against the schema, and refine their analysis based on structured feedback. This makes graph-based systems a better fit for advanced use cases such as automated investigation and GraphRAG pipelines.
Conclusion
Modern environments, being dynamic and deeply interconnected, require the structural discipline an AI security graph provides to elucidate critical risks that otherwise remain hidden in plain sight.
Despite the appeal, the challenge mostly has been the cost and complexity of building and maintaining it, namely separate pipelines that you have to maintain and duplicated data. Both of these slow teams down and introduce new failure points.
PuppyGraph enables graph analysis directly on existing data, without re-architecting your stack. The result is faster insight, lower overhead, and a clearer view of how your systems actually behave.
To see how PuppyGraph makes AI security graphs more accessible for enterprises, grab PuppyGraph’s forever-free Developer Edition, or book a demo.
Get started with PuppyGraph!
Developer Edition
- Forever free
- Single noded
- Designed for proving your ideas
- Available via Docker install
Enterprise Edition
- 30-day free trial with full features
- Everything in developer edition & enterprise features
- Designed for production
- Available via AWS AMI & Docker install





