What Is On-Path Attack?
Your network traffic passes through dozens of intermediary systems before reaching its destination. On-path attackers who position themselves at any one of those points can intercept communications between two parties, reading, modifying, or redirecting data without either side knowing. This is an on-path attack, and it remains one of the most dangerous and difficult-to-detect threats in network security.
On-path attacks, previously known as man-in-the-middle (MITM) attacks, exploit weaknesses in authentication, integrity verification, and trust within network communication. In reality, data hops through routers, switches, DNS resolvers, and proxy servers. Each hop is a potential interception point. An attacker who controls or compromises any of these intermediaries may gain unauthorized access to sensitive data passing through the communication channel, from login credentials to financial records, depending on the encryption and protocol protections in place.
What makes on-path attacks particularly dangerous is that data interception of this kind is difficult to detect using traditional log-based monitoring and network monitoring tools. The signals exist (TLS warnings, ARP anomalies, DNS inconsistencies), but they are subtle and distributed across multiple systems. The attacker doesn't break into a system; they sit between systems. SIEM tools that analyze events one row at a time struggle to correlate the relational pattern: a DNS resolution that points somewhere new, a certificate that changed on one hop, a session token reused from an unexpected subnet. These are connected events, and spotting the connection requires modeling your network as a graph.
This is why security teams are adopting graph-based approaches to attack surface management. When network assets and communication paths are represented as nodes and edges, on-path intrusions become structurally visible. The attacker may introduce a new intermediary node or alter existing communication paths in ways that graph queries can detect.
How On-Path Attacks Work
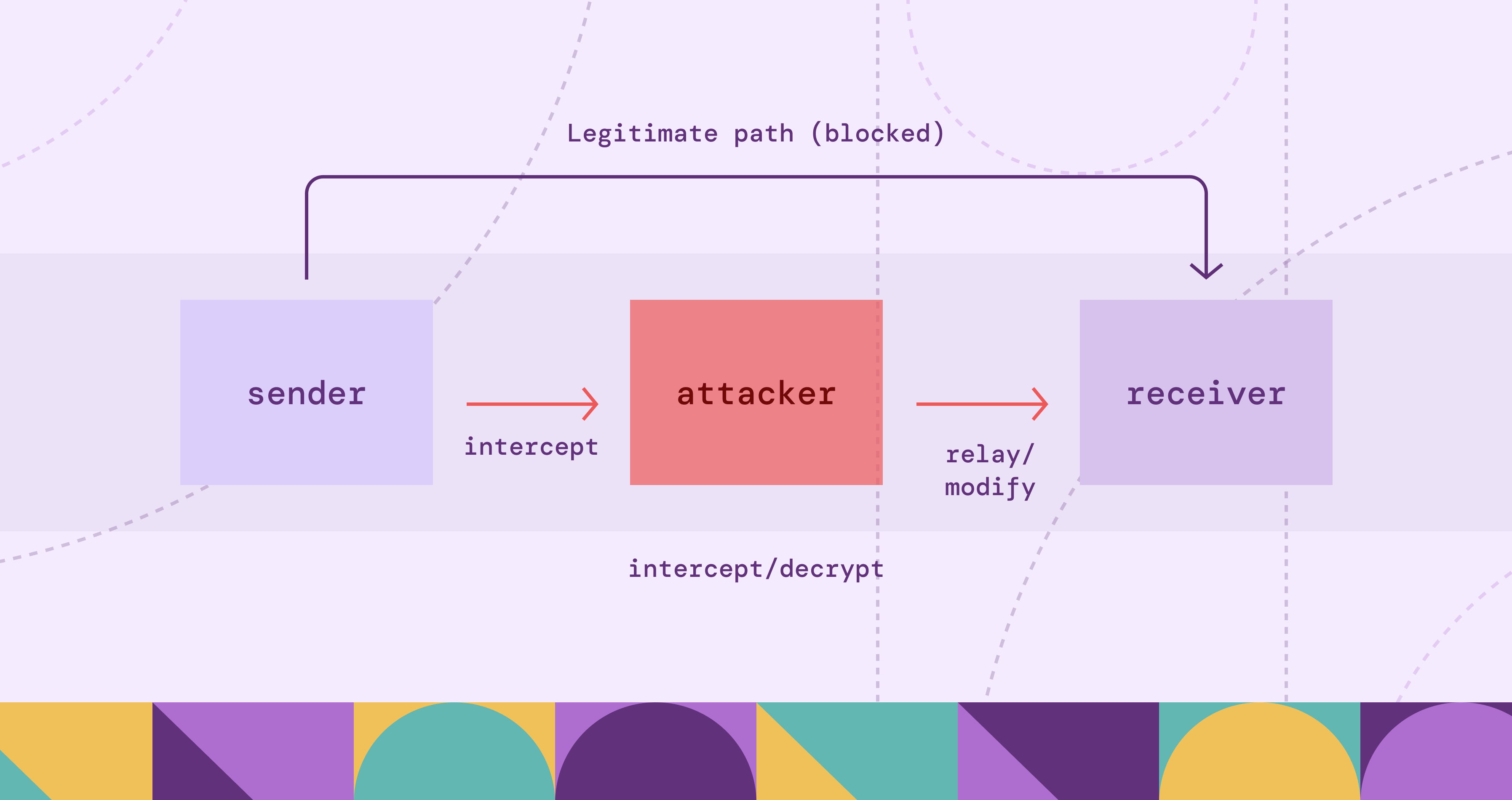
When an on-path attack occurs, it follows a consistent pattern regardless of the specific technique used.
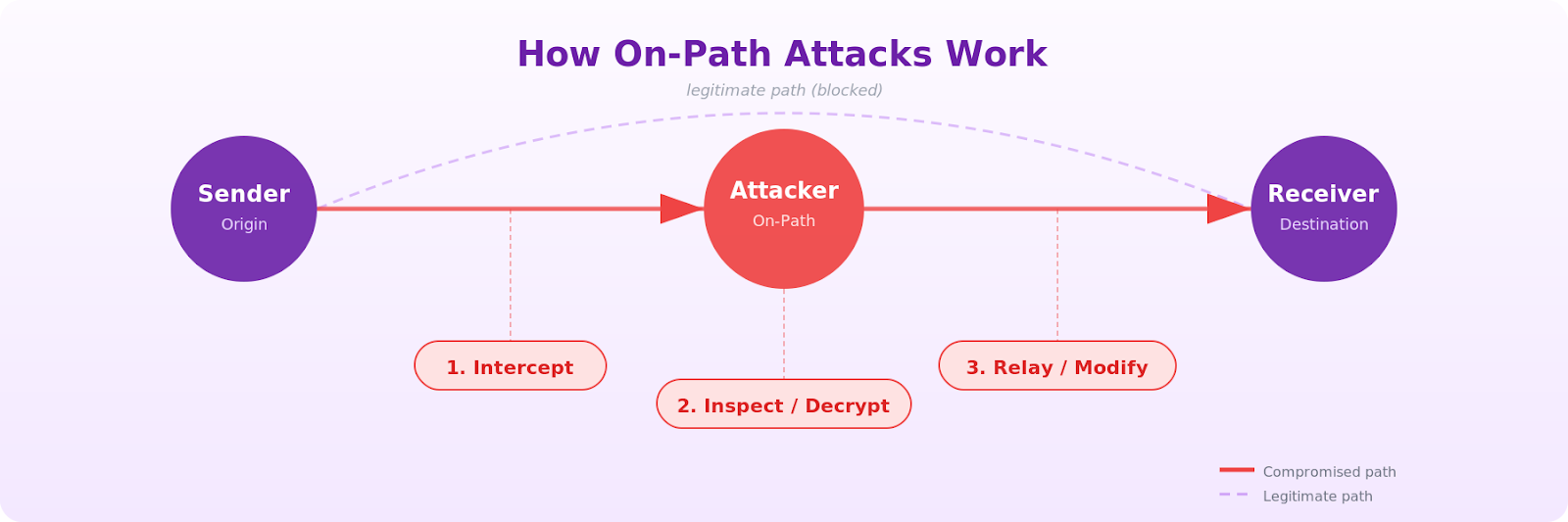
The attacker secretly intercepts legitimate communications by gaining a position along the data transmission path between two communicating parties, then exploits that position to intercept data, read it, or alter the data flowing between them.
The attack unfolds in three stages:
Interception. The attacker redirects network traffic through a system they control. This might involve poisoning a DNS cache so domain lookups resolve to the attacker's IP, spoofing ARP responses on a local network, or setting up a rogue WiFi access point that mimics a trusted network. The victim's device believes it is communicating with the intended destination, but traffic is being routed through the attacker.
Decryption or inspection. Once traffic flows through the attacker's system, they need to read it. For unencrypted HTTP traffic, this is trivial. For encrypted HTTPS connections, the attacker may attempt to downgrade encryption, impersonate endpoints with forged certificates, or exploit misconfigured TLS implementations. Modern TLS with proper certificate validation makes this significantly harder, but not impossible, when users accept certificate warnings or when systems rely on outdated cryptographic configurations. Even when encryption holds, the attacker can still observe metadata: which servers the victim contacts, when, and how frequently.
Action. With access to the data stream, the attacker can passively record sensitive information (credentials, session cookies, personal data) or actively manipulate data in the data packets as they pass through. Active modification might include injecting malicious scripts to redirect users to fake websites, altering financial data in transaction details, or modifying email content before it reaches the recipient. The attacker possibly alters transmitted data or inserts harmful code, and the entire process can happen in milliseconds, with neither party aware that their communication has been compromised.
Types of On-Path Attacks
On-path attacks vary in technique, but such attacks all achieve the same goal: positioning the attacker between two communicating endpoints.
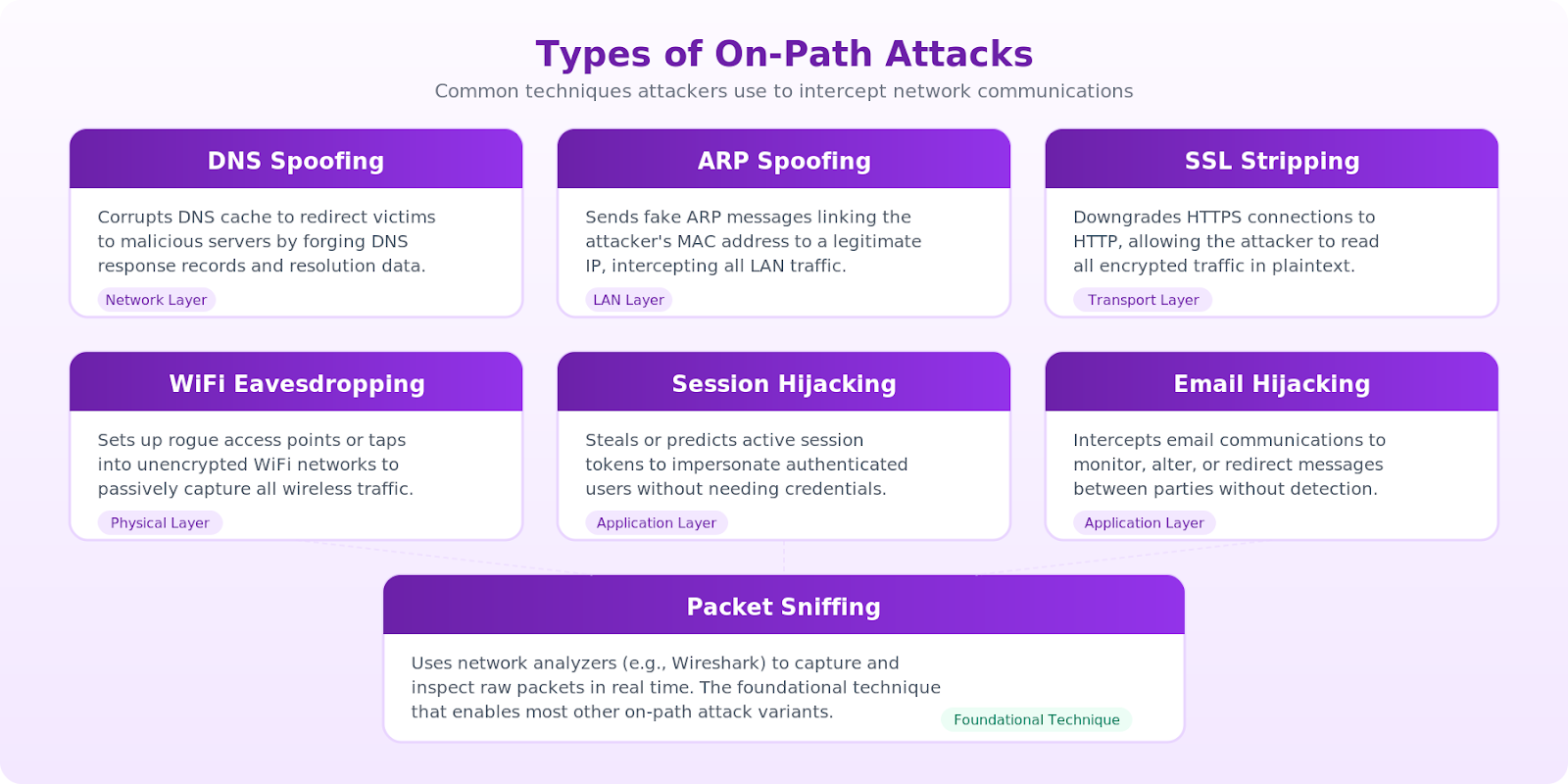
Each type targets a different layer of the network stack.
DNS Spoofing
DNS spoofing corrupts the domain name resolution process. An attacker poisons a DNS cache or forges DNS responses so that when your browser requests the IP address of your bank's website, it receives the IP address of a server the attacker controls. Your browser connects to the attacker's server, which presents a convincing replica of the bank's login page. You enter your credentials, and the attacker captures them while forwarding the request to the real bank, so you never notice.
ARP Spoofing
Address Resolution Protocol (ARP) maps IP addresses to physical MAC addresses on local networks. An attacker sends falsified ARP messages to associate the attacker's MAC address with the network gateway's IP. All traffic from devices on the network then routes through the attacker's machine before reaching the actual gateway. This attack is limited to local area networks but highly effective in corporate environments and shared workspaces.
SSL Stripping
SSL stripping downgrades a secure HTTPS connection to unencrypted HTTP. The attacker intercepts the initial connection and communicates with the target server over HTTPS while serving the user an HTTP version. All data between the user and attacker travels in plaintext. This technique is less effective today due to widespread HSTS adoption and browser protections, but it still works against sites that haven't implemented HSTS or on the first visit before a browser has cached the HSTS policy.
WiFi Eavesdropping
WiFi eavesdropping targets public WiFi networks and unsecured WiFi networks. An attacker creates rogue access points on wireless networks with a name identical to a legitimate network ("Airport_Free_WiFi" or "Starbucks_Guest"). Users connect to the rogue access point, and all their traffic passes through the attacker's hardware. This is one of the simplest on-path attacks to execute and one of the most common in public spaces, which is why connecting to secure WiFi networks matters.
Session Hijacking
After a user authenticates with web applications, the server issues a session token tied to the user's session. An attacker who intercepts this token can impersonate the authenticated user without needing their password. This can bypass multi-factor authentication in many implementations because the hijacking occurs after authentication completes, though modern defenses like token binding and device fingerprinting are narrowing this gap.
Email Hijacking
Attackers who gain on-path access between email servers, or who combine on-path interception with account compromise, can read, modify communications, or redirect private messages. In targeted business email compromise (BEC) attacks, the attacker monitors email threads about pending financial transactions, then injects a message with altered payment instructions. The recipient wires funds to the attacker's account, believing the email came from a trusted contact.
Packet Sniffing
Packet sniffing is the passive form of an on-path attack. When positioned on the communication path or within a shared network segment, the attacker captures network packets without modifying them, harvesting credentials, session tokens, API keys, and any data transmitted in plain text.
On-Path Attack vs Man-in-the-Middle
The terms refer to the same category of attack. "Man-in-the-middle attack" (MITM), sometimes shortened to "middle attack," was the original name, and you will still encounter it frequently in older documentation, certification materials, and security tools. The industry has been shifting toward "on-path attack" as the preferred terminology for two reasons.
First, "on-path" more accurately describes what happens technically. The attacker positions themselves on the communication path between two endpoints. The "middle" framing implies a single fixed position, when in practice the attacker might be at any point along the route. Second, the industry has moved toward more inclusive technical language.
From a defensive standpoint, the distinction is purely nomenclature. The techniques, risks, and mitigations are identical regardless of which term you use. When searching for detection signatures or security advisories, search for both terms to ensure complete coverage. Many vulnerability databases and SIEM rules still reference MITM.
Risks and Consequences of On-Path Attacks
The damage from a successful on-path attack extends far beyond the immediate data theft. Because the attacker occupies a position of trust within the communication flow, the consequences compound across systems and over time, often leading to data breaches and security breaches that affect the entire organization.
Credential theft and lateral movement. Intercepted credentials give the attacker initial access, but that is rarely where they stop. Attackers move laterally across the network, escalating privileges and accessing increasingly sensitive systems. A single intercepted VPN login can lead to access across an organization's entire internal infrastructure.
Financial fraud. Business email compromise (BEC) attacks, where the attacker modifies wire transfer instructions mid-conversation, routinely cause losses ranging from tens of thousands to millions of dollars per incident, according to FBI IC3 reporting.
Data exfiltration. An attacker with persistent on-path access can silently siphon valuable data over weeks or months, including financial data, identity theft targets like personal records, and intellectual property. This slow exfiltration is harder to detect than a smash-and-grab breach because the volume blends with normal traffic patterns.
Supply chain compromise. When on-path attacks target communications between organizations and their vendors, the blast radius expands to every entity in the supply chain. Modified software updates enabling malware distribution, or tampered API responses, cascade through interconnected systems.
The core problem is that on-path attacks create chains of compromised relationships across your infrastructure. A credential stolen from one system connects to lateral movement in another, which connects to data access in a third. In a SIEM, each event sits in a separate log stream. An analyst would need to manually join them, often across hours of investigation.
In a graph model, these connections are explicit. Every compromised credential, lateral hop, and data access event is a node connected by edges: STOLEN_FROM, USED_TO_ACCESS, ESCALATED_TO. Graph-based threat detection can turn a multi-hour correlation exercise into a single graph traversal. A breadth-first search (BFS) query from the initial interception point can reveal every asset the attacker touched and the path they took. Instead of investigating alerts one at a time, security teams can see the full blast radius in seconds.
How to Detect On-Path Attacks
Detecting an on-path attack is difficult precisely because the attacker's goal is to remain invisible. The communication appears normal to both parties. However, on-path attacks do leave subtle indicators that intrusion detection systems and the right monitoring approach can catch. The key is deploying systems that analyze network traffic holistically rather than alert-by-alert.
Certificate anomalies. Monitor for unexpected certificate changes on frequently accessed domains, certificate authority mismatches, or connections that downgrade from HTTPS to HTTP. Certificate transparency logs can reveal unauthorized certificate generation.
ARP table inconsistencies. On local networks, duplicate MAC address entries or frequent ARP table changes can indicate ARP spoofing. Tools that baseline normal ARP behavior and alert on deviations catch most ARP-based on-path attacks.
DNS response validation. DNSSEC cryptographically signs DNS responses, making spoofed responses detectable. Even without full DNSSEC deployment, monitoring for DNS responses that arrive faster than expected or contain unexpected IP addresses can flag spoofing attempts.
Latency anomalies. An on-path attacker adds a hop to the communication path. In some cases, statistical analysis of connection timing over a baseline period can reveal consistent, slight delays that indicate interception, though this signal tends to be noisy and works best as a supporting indicator alongside other detection methods.
Graph-based traffic flow analysis. This is where detection shifts from reactive to structural. Individual alerts about certificate changes, DNS anomalies, or latency spikes are noisy in isolation. But when you model network communications as a graph, with assets as nodes and traffic flows as edges, the pattern becomes queryable.
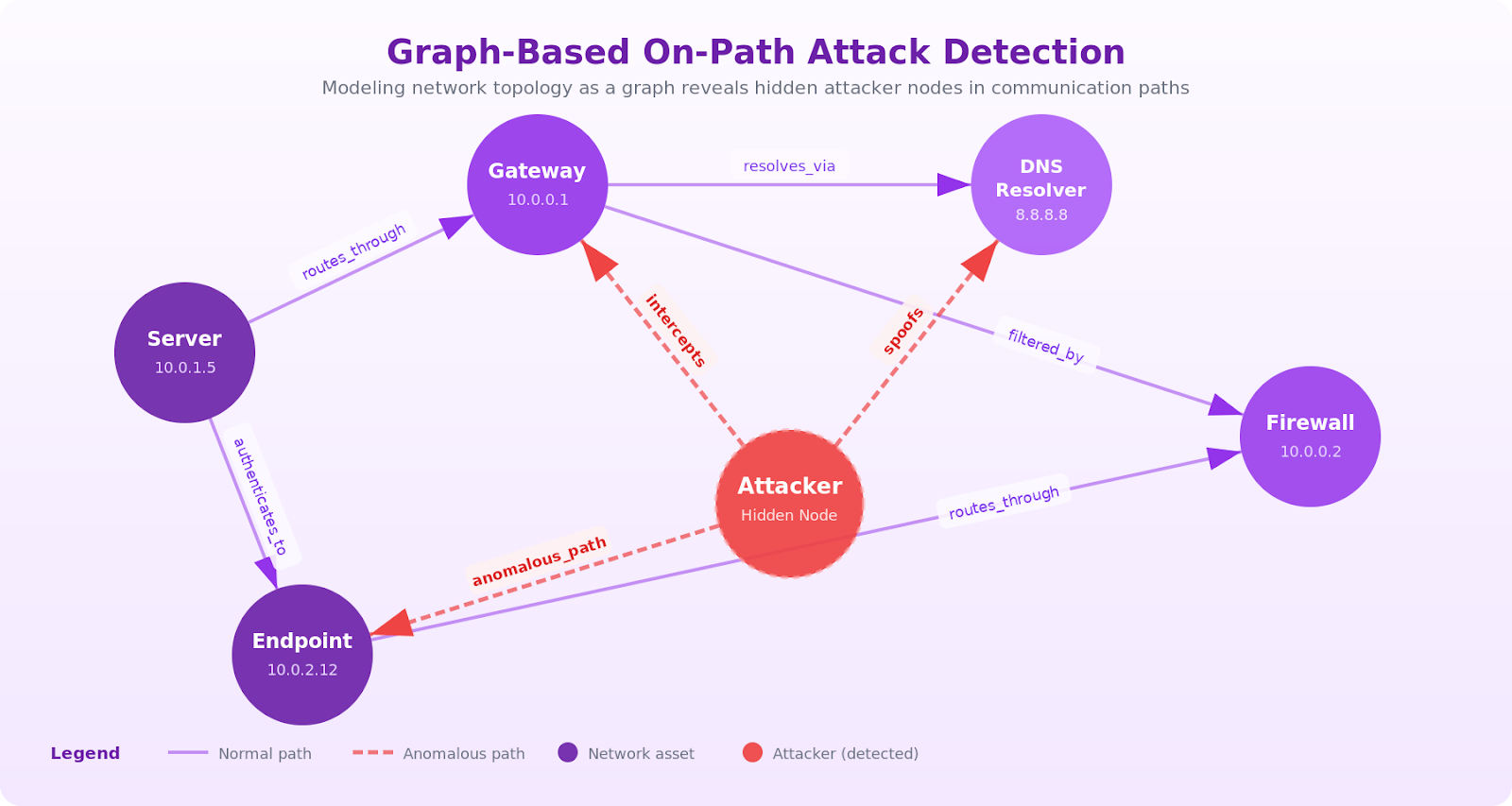
Your network graph has nodes for every server, endpoint, DNS resolver, and gateway, connected by edges representing normal traffic flows. When an on-path attacker inserts themselves, a new node appears between two endpoints that previously communicated directly. A graph query engine like PuppyGraph detects this structural change with a path query: find all paths between endpoint A and server B where the hop count increased compared to the baseline. That query can run in sub-second time, even across large-scale network telemetry, because PuppyGraph's zero-ETL architecture queries your existing data stores directly.
The same approach catches subtle multi-signal patterns. Three unrelated anomalies (a DNS response from an unexpected resolver, a certificate mismatch on a subnet, a latency spike on a gateway) all converge on the same intermediary IP. In a log-based system, these are three separate alerts. In a graph, there are three edges pointing to the same suspicious node. A single Cypher or Gremlin query can surface the connection in seconds.
Prevention Strategies for On-Path Attacks
Preventing on-path attacks requires a layered approach that establishes secure connections and secure communication channels across your infrastructure. No single control eliminates the risk, but the combination of strong encryption, network controls, and continuous monitoring reduces the attack surface substantially.
Enforce HTTPS everywhere. Deploy TLS across all web properties and internal services, not just login pages. Use HTTP Strict Transport Security (HSTS) headers to tell browsers to always connect over HTTPS, preventing SSL stripping. Preload your domains into browser HSTS lists for protection from the very first connection.
Implement certificate pinning and public key infrastructure. Certificate pinning binds a specific certificate or public key hashes to a domain through public key infrastructure (PKI), preventing an attacker from substituting their own certificate even if they've compromised a certificate authority. This is particularly important for mobile applications and API clients that communicate with known backend servers.
Deploy DNSSEC. DNSSEC adds cryptographic signatures to DNS records, allowing resolvers to verify that responses haven't been tampered with. While adoption has been slow, DNSSEC eliminates DNS spoofing as an attack vector for protected domains.
Secure local networks. Use 802.1X port-based authentication to prevent unauthorized devices from joining the network. Deploy Dynamic ARP Inspection (DAI) on switches to validate ARP packets against a trusted binding table. Apply network segmentation to limit the blast radius of any local compromise and to identify vulnerabilities before attackers can exploit them.
Require virtual private networks for remote access. Virtual private networks (VPNs) provide end-to-end encryption for all traffic between the user's device and the corporate network, establishing secure communication and significantly reducing the risk of WiFi eavesdropping and packet sniffing on untrusted networks. Ensure VPN configurations use strong cipher suites and guard against DNS leaks.
Build a cybersecurity knowledge graph. Prevention controls will always have gaps. The question is how fast you find what slipped through. Traditional detection stacks force analysts to pivot between disconnected tools: SIEM for logs, CMDB for asset inventory, vulnerability scanners for exposure data. Each tool holds a piece of the puzzle, but none model the relationships between pieces.
A cybersecurity knowledge graph unifies these sources into a single queryable model. Assets, users, network paths, and security events become nodes. The relationships between them (ROUTES_THROUGH, AUTHENTICATED_VIA, ISSUED_BY) become edges. When an on-path attacker alters any of these relationships, the structural change is detectable through graph traversal.
PuppyGraph is built for this use case. Its zero-ETL architecture queries your data where it already lives (Snowflake, Databricks, PostgreSQL, S3) and returns results in sub-second time. Write detection queries in openCypher or Gremlin, and PuppyGraph handles the cross-source joins that would otherwise take weeks to build. Security teams at companies like Coinbase and Netskope use this approach to map attack surfaces and detect anomalous network topology changes in real time.
Conclusion
On-path attacks exploit the fundamental trust model of network communication. They are versatile, difficult to detect with traditional tools, and capable of causing damage that extends far beyond the initial interception. The shift in terminology from "man-in-the-middle" to "on-path attack" reflects not just a language update but also growing recognition that these attacks target the path itself, not a single point.
Defending against on-path attacks requires encryption, network controls, and a detection layer that thinks the way attackers do: in graphs. Attackers don't operate in rows and columns. They traverse networks, hopping from one compromised asset to the next along paths of least resistance. Detecting them means modeling those same paths and querying for the structural anomalies they introduce.
Graph analytics gives security teams this capability. By representing your network topology and traffic patterns as a connected graph, you can ask questions that are impossible in traditional monitoring: "Show me every path between this endpoint and this server that passes through a node added in the last 24 hours." "Find all assets reachable within two hops of this compromised credential." These are the kinds of queries that can catch on-path attacks before the attacker has time to exfiltrate data.
PuppyGraph's graph capabilities for cybersecurity make this approach accessible without a multi-quarter data engineering project. Connect to your existing data stores, define your graph schema, and start querying in minutes. No ETL pipelines, no data duplication. Direct, fast graph queries over the security data you already have.
Want to try it for yourself? Explore PuppyGraph’s forever-free Developer Edition or book a demo to get started.




