What Is External Attack Surface Management?

Every organization that operates online has a digital footprint — and that footprint is growing faster than most security teams can track. Every new cloud service spun up, every web application deployed, every API published to the internet adds another piece to what security professionals call the external attack surface. Left unmonitored, this surface becomes a sprawling landscape of potential entry points for attackers.
External Attack Surface Management (EASM) is the discipline that addresses this challenge head-on. It gives security teams the tools, processes, and visibility needed to continuously discover, monitor, and reduce risk across every internet-facing asset their organization owns — whether they know about it or not.
This guide breaks down what EASM is, why it matters, how it works in practice, and what organizations stand to gain by making it a core part of their security program.
What Is External Attack Surface Management?
At its core, External Attack Surface Management is the ongoing process of identifying, inventorying, and monitoring all digital assets that are exposed to the public internet — and then assessing those assets for vulnerabilities, misconfigurations, leaked credentials, or any other conditions that could be exploited by a malicious actor.
This sounds straightforward, but the reality is complex. Modern organizations don't always have a perfect picture of what they've published to the internet. Shadow IT, forgotten subdomains, misconfigured cloud storage buckets, third-party integrations, and acquisitions all contribute to an external attack surface that can be far larger than IT or security teams realize. EASM tools are specifically designed to discover these assets from the outside — just as an attacker would — and map them to the organization that owns them.
The goal isn't simply to build an asset inventory. The real value of EASM lies in continuous monitoring: understanding how the external attack surface changes over time, detecting new exposures the moment they appear, and enabling security teams to act before attackers do.
Beyond asset discovery, EASM encompasses monitoring for a range of external risk signals including open ports, expired certificates, public cloud misconfigurations, leaked credentials appearing on the dark web, and software vulnerabilities in publicly accessible systems. It aligns closely with the objective of maintaining a clear and accurate picture of an organization's cloud security posture at all times.
How External Attack Surface Management Works
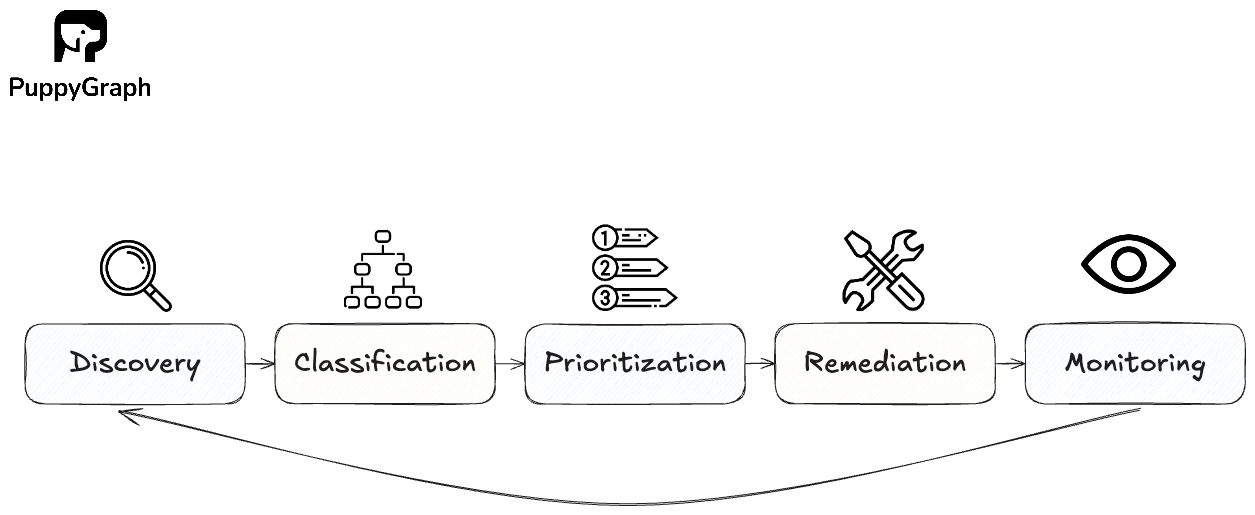
EASM consists of five stages: Discovery, Classification, Prioritization, Remediation and Monitoring. Let’s dive deeper into how they work to provide a live view of your asset inventory.
Discovery
Discovery is the starting point for any EASM program. An EASM platform starts with what you already know, then works outward across your real footprint. It takes your official domains, IP ranges, and key web applications as seeds, then uses DNS lookups, Certificate Transparency logs, IP intelligence, and scanning to uncover everything on the internet that appears to belong to you, from mail servers and exposed RDP to forgotten microsites, test environments, and misconfigured cloud services. It is also at this stage that normalization occurs, so the same system is not counted three different ways.
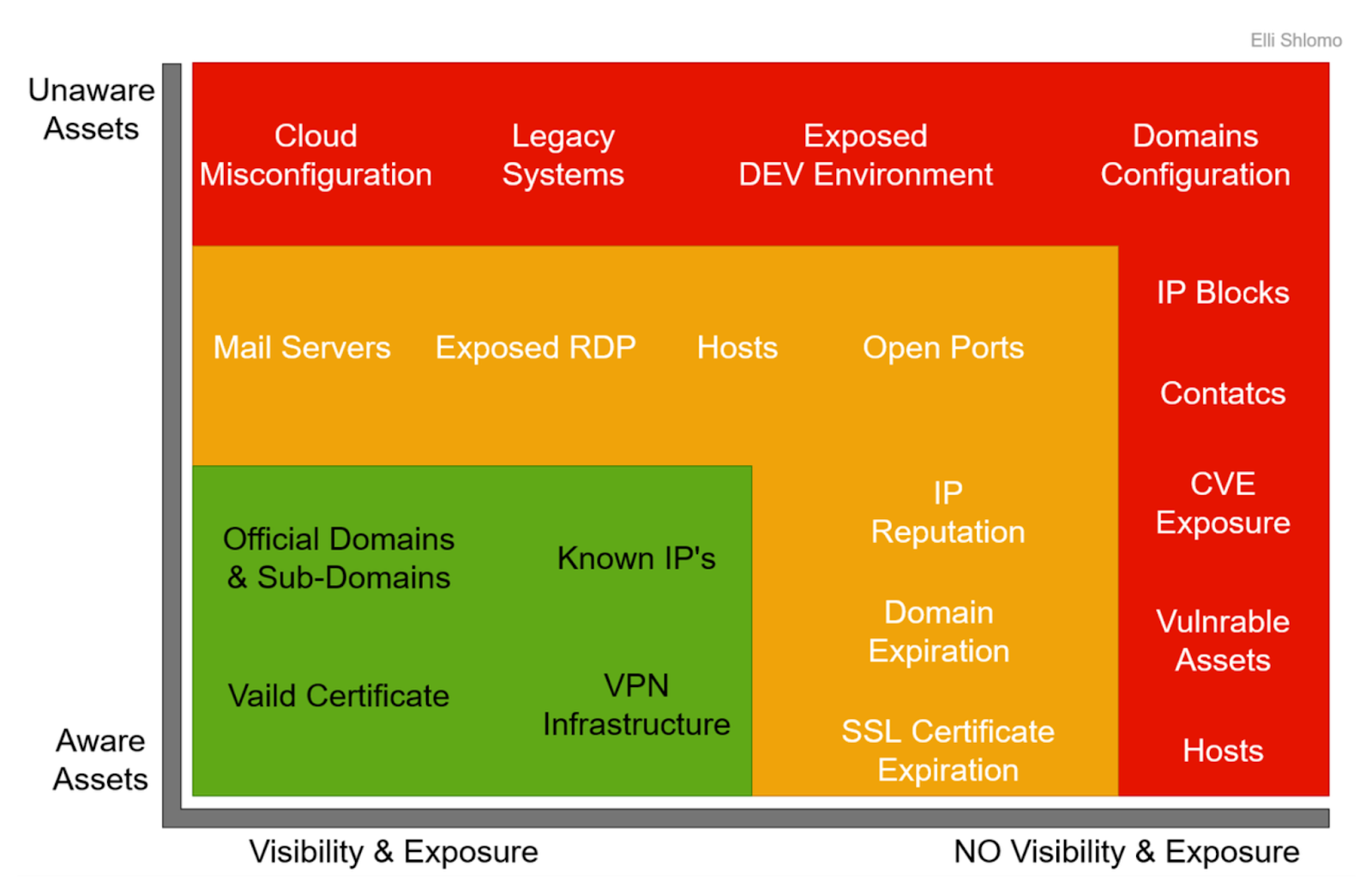
The result is an outside in view of your organization, the same view an attacker would have when they start recon. By turning more of the external footprint into known and observable assets, security teams can decide what they can fix directly, what needs to be addressed through partners or vendors, and where new risk is quietly accumulating over time.
Classification
Classification adds the context that tells you what each asset is and who should care. An EASM platform enriches discovered hosts, domains, and endpoints with technical details like asset type, network information, and registration details. It also captures traits like whether the asset requires authentication, what tech stack it runs on, and whether it is meant to be user facing or was an internal tool that ended up on the public internet.
With this structured context, security teams can build an asset graph that connects domains, IPs, certificates, services, cloud accounts, and owners into a single, queryable view.
Prioritization
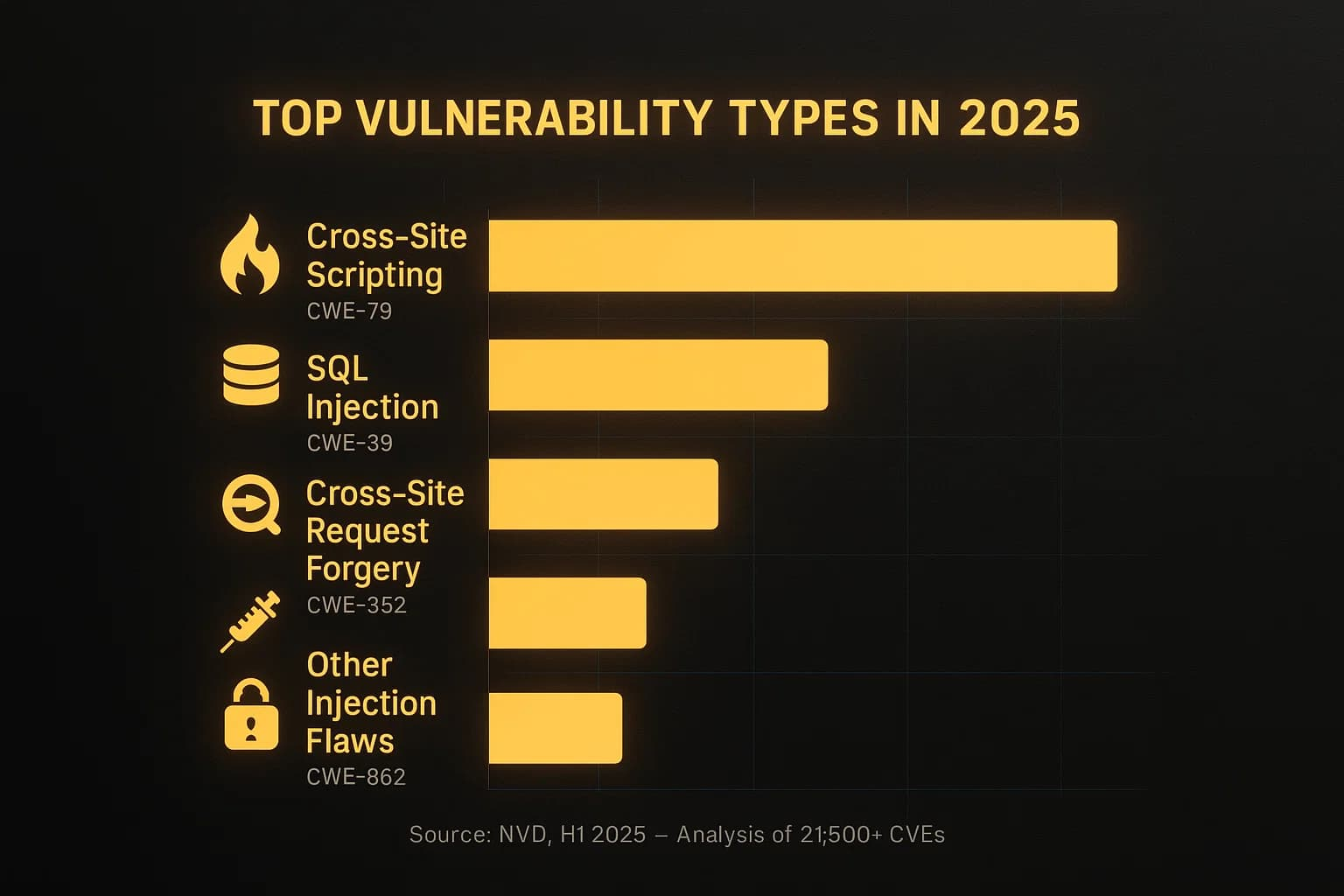
In an EASM program, prioritization ranks findings so teams know where to focus. Platforms use fast signals to assign an initial severity, drawing on exploitability, reachability from the internet, business context, data sensitivity, and signs of active abuse.
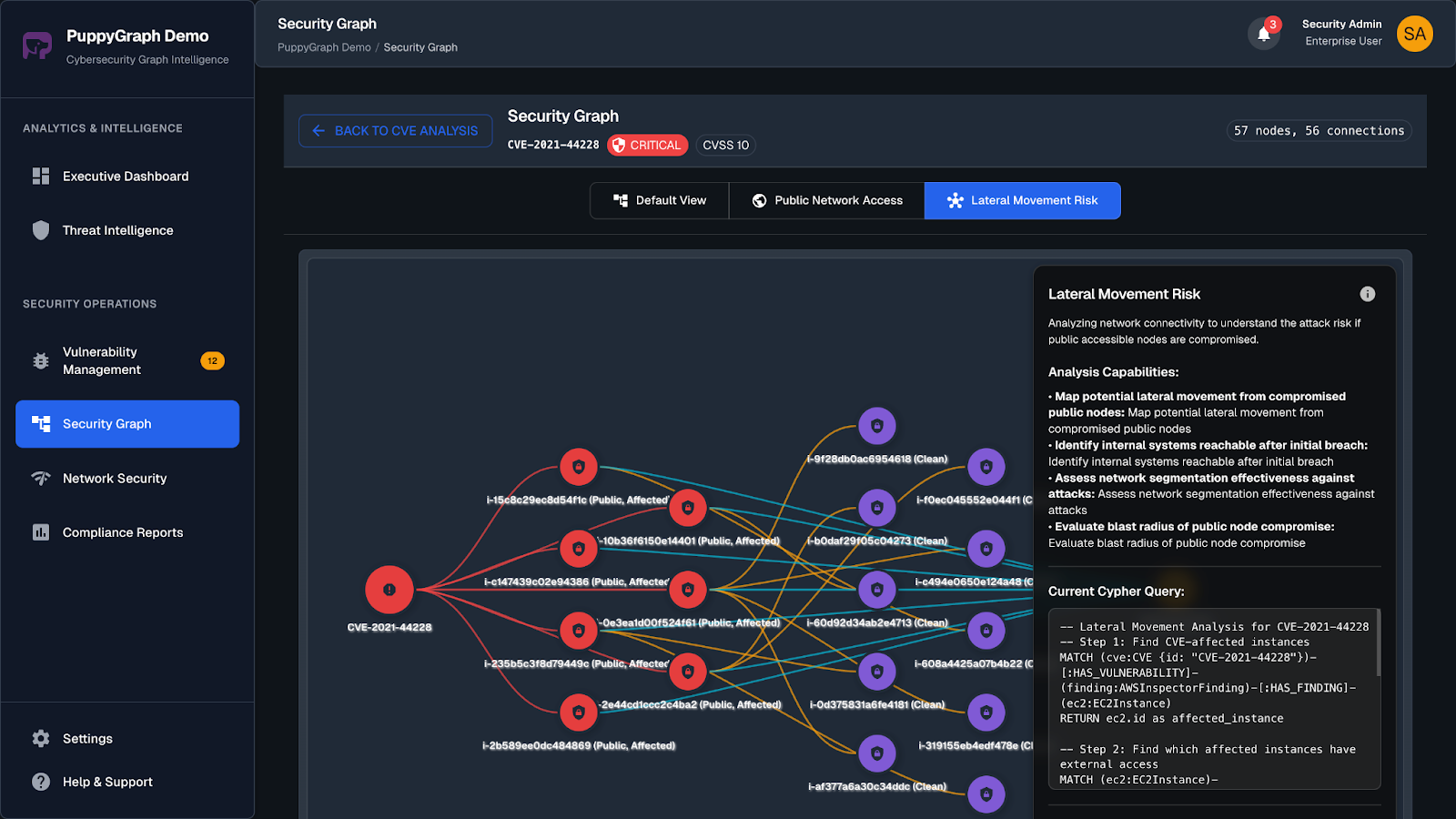
Many cybersecurity platforms have started introducing a graph layer to enable context-enriched ranking, where assets are nodes and relationships include things like domain to subdomain links, shared IPs or certificates, and paths from internet facing entry points to backend services or admin portals. This ties findings to real attack paths, so the issues at the top of the list are the ones that threaten business critical systems and data.
Remediation
Remediation is where EASM turns a ranked list of issues into concrete changes. When integrated into your workflows, EASM tools route each problem to the right owner, provide the context needed to fix it quickly, and then rescan from the outside to confirm the issue is no longer exposed.
Monitoring
Monitoring is what keeps EASM from turning into a one time cleanup. Once fixes land, the same external view is used to watch for new assets, configuration drift, and regressions. Over time, this gives security teams a feedback loop: they can see whether controls are holding, which teams or environments keep reintroducing the same issues, and whether the attack surface is growing faster than they are closing gaps.
Key Capabilities of External Attack Surface Management
Modern EASM platforms do more than crawl the internet for stray subdomains. They combine a few core capabilities that turn external visibility into something security teams can act on.
Unified External Asset Inventory
Modern EASM tools maintain a consolidated view of public facing assets: domains, subdomains, IPs, web apps, APIs, cloud endpoints, and SaaS entry points. Instead of scattered scans, they present a single inventory that shows what is exposed and how it fits into the rest of the environment.
Continuous Monitoring
The external attack surface is always changing, so current tools focus on continuous monitoring rather than one off projects. They watch DNS, certificates, exposed services, and cloud resources for changes, updating the inventory as new assets appear or old ones are reconfigured.
Faster, Context-Aware Prioritization
EASM platforms help teams decide what to fix first. They order findings using signals like exploitability, reachability from the internet, business context, data sensitivity, and signs of active abuse. Increasingly, they add simple attack path context so exposures that sit in the path of critical systems rise to the top.
Workflow-friendly Integrations
Modern EASM does not live in isolation. It integrates with data sources such as SIEM and EDR for richer context and connects to ticketing systems like Jira or ServiceNow so findings turn into trackable work items. APIs and webhooks allow teams to plug EASM data into their existing automation and reporting, making external visibility part of the broader security workflow.
EASM vs Traditional Vulnerability Management
EASM and traditional vulnerability management (VM) solve related but different problems. VM grew up around known, managed assets: servers, workstations, and applications that already live in an inventory. You install agents or run authenticated scans, then look for missing patches and misconfigurations. EASM starts one step earlier. It asks what is exposed to the public internet in the first place, including assets that never made it into a CMDB or scan target list.
In practice, many vendors now bundle EASM and vulnerability management into a single platform.This reflects a broader shift toward unifying separate security tools into a single platform, so organizations can see their security posture in one place.
Challenges in External Attack Surface Management
EASM is powerful, but it can still suffer from coverage gaps, noisy findings and operational constraints that teams need to plan for.
Incomplete Coverage and Blind Spots
EASM relies on what is visible from the public internet. Assets behind strict IP allowlists, VPN only portals, or private front doors may not appear in its results. Some providers also expose very little metadata, which makes certain cloud and SaaS surfaces hard to map. This means attackers can sometimes see paths or combinations of assets that the EASM platform misses, especially in very large or fragmented environments.
Attribution and Ownership Mapping
Finding an exposed asset is only half the problem. Figuring out who owns it is another. Legacy domains, orphaned subdomains, old IP ranges, and assets inherited through mergers or reorganizations often have no clear team attached. Without reliable ownership mapping, issues bounce between teams, stall in triage, or never reach the people who can actually fix them, even when the exposure is obvious.
Noise and Shallow Findings
Because EASM usually works without credentials, it is limited to what it can see from the outside. Unauthenticated checks can misjudge risk if they cannot see internal controls or compensating defenses. Some findings are low confidence or noisy, which can reduce trust if they are not clearly labeled. EASM is good at flagging obvious exposure on internet facing assets, but might require more context for patch-level detail.
Limited Control over Third Party and Shared Assets
EASM often surfaces risks on infrastructure that you do not fully control. Vendor portals, white label apps, and shared SaaS environments may look like your organization to users and attackers, but sit on someone else’s stack. Fixing those issues can require vendor support tickets or contract changes. In many cases, the only levers you have are how you point to the service, how you authenticate to it, and whether you continue to use it at all.
How To Implement External Attack Surface Management
To fully leverage the potential of your EASM tools, security teams need a plan that starts small, builds ownership, and turns findings into fixes.
Start with a Clear Scope and Goal
EASM works best when it targets a specific problem instead of trying to cover everything at once. Pick a focused starting point such as core domains, a single business unit, or a few cloud accounts. Run EASM there, show that it can reliably discover assets, assign ownership, and close issues, then expand. A smaller, well scoped rollout builds trust and avoids overwhelming teams with more findings than they can handle.
Fix Ownership and Tagging Early
Unknown owners are where exposures linger. EASM tools can automate a lot of the heavy lifting, but human input is still crucial to confirm these assignments and add real context. Even a rough owner is better than none, and this mix of automated suggestions and human review turns findings into actionable work instead of tickets that bounce between teams with no clear responsibility.
Tune Noise and Validate Findings
External only checks are never perfect, so expect some noise. Graph analytics can help here by grounding findings in real context, highlighting exposures that sit on actual paths to sensitive systems and pushing down vulnerabilities that are purely theoretical. Mark low confidence or low impact findings so they do not drown out real issues, and suppress patterns you agree are acceptable risks. The goal is a queue that engineers trust, backed by clear evidence from the external view instead of a maximum volume of alerts.
Choosing the Right External Attack Surface Management Tool
Here’s a quick checklist to consider the best ASM tools for your needs:
- Discovery depth and frequency: Continuous discovery with near real-time updates is preferred. Mix passive recon, active scans, cert and DNS monitoring to build a complete and accurate inventory.
- Asset coverage: Handles the assets you care about across hybrid and multicloud. Domains, subdomains, IPs, cloud services, APIs, certs, SaaS, and external services.
- Risk context and scoring: Scoring that blends exploitability, reachability, threat intel, and business importance. They should be tunable to your risk tolerance.
- Integrations and workflow: Make sure it plugs into where you scan and where you work. For scanning, this includes APIs for cloud, SaaS and WAFs. For workflow, SIEM, SOAR, VM, CSPM, and ticketing.
- Change detection and history: Near real-time alerts on high-risk changes with a timeline of what changed and when.
- Deployment: Fast onboarding, sane authentication and network requirements, with cloud or on-prem options.
Conclusion
External attack surface management gives security teams an attacker’s eye view of their organization. It discovers what is actually exposed on the internet, adds enough context to understand what each asset is and who owns it, then helps teams prioritize and fix the issues that matter most.
At the same time, EASM struggles with context. This is where PuppyGraph fits. It lets you build and query an attack graph directly on top of your existing security and infrastructure data, without standing up a separate graph database or building fragile ETL pipelines. You get real time, multi hop analysis across SIEM, cloud, identity, and asset data, so EASM findings are ranked and investigated in the context of how an attacker would actually move through your environment.
When you layer in relationships between assets, data, and identities, you can trace real attack paths and focus on exposures that truly put critical systems and data at risk instead of chasing every theoretical vulnerability.
If you want to see this in your own data, you can try PuppyGraph’s forever-free Developer Edition or book a demo with the team to walk through your use cases live.
Get started with PuppyGraph!
Developer Edition
- Forever free
- Single noded
- Designed for proving your ideas
- Available via Docker install
Enterprise Edition
- 30-day free trial with full features
- Everything in developer edition & enterprise features
- Designed for production
- Available via AWS AMI & Docker install




